JWT, IAM, and Auth0: Authentication and Authorization Explained (Without the Confusion)
Modern applications rarely live in one place. A typical product spans web apps, mobile apps, APIs, microservices, third-party integrations, and multiple cloud environments. In that world, the question isn’t just “Who are you?”-it’s also “What are you allowed to do?” and “How do we prove it securely across systems?”
That’s where authentication, authorization, JWT, IAM, and platforms like Auth0 come in. These terms are often used interchangeably (incorrectly), which leads to brittle security designs, over-permissive access, and painful rework.
This guide breaks the concepts down clearly, shows how they connect, and provides practical examples you can apply to real architectures.
Authentication vs. Authorization (The Most Important Distinction)
What is Authentication?
Authentication is the process of verifying identity.
- “Are you really Alice?”
- Common methods: username/password, MFA, passkeys, biometrics, social login, SSO
Output: a verified identity (a “principal” or user).
What is Authorization?
Authorization is the process of determining access permissions.
- “Can Alice view invoices?”
- “Can Alice delete users?”
- “Can this service call that API endpoint?”
Output: a yes/no decision (often paired with constraints like scopes, roles, or policies).
In short:
- Authentication = who you are
- Authorization = what you can do
What Is IAM? (Identity and Access Management)
IAM (Identity and Access Management) is the broader discipline and system set for managing identities and controlling access-across users, devices, services, and workloads.
Think of IAM as the umbrella that typically includes:
- Identity lifecycle (user provisioning/deprovisioning)
- Authentication mechanisms (SSO, MFA, passwordless)
- Authorization models (RBAC, ABAC, policy-based access)
- Directory services and user stores
- Audit logs and compliance reporting
- Secrets, keys, and credential policies (in many organizations)
IAM in Practice
In an enterprise environment, IAM answers questions like:
- How do employees sign in to all internal tools using SSO?
- How do contractors lose access automatically when a contract ends?
- How do APIs authenticate services calling each other?
- How do you enforce least privilege across thousands of permissions?
What Is a JWT? (JSON Web Token)
A JWT (JSON Web Token) is a compact, URL-safe token format commonly used to represent claims about a user or client-often for API access.
A JWT typically contains three base64url-encoded parts:
- Header (token type + signing algorithm)
- Payload (claims like user ID, issuer, audience, expiration, roles/scopes)
- Signature (verifies integrity and authenticity)
Why JWTs Are Used So Often
JWTs are popular because they’re:
- Stateless (APIs can validate them without a database lookup)
- Portable (easy to pass via HTTP headers)
- Verifiable (signed; sometimes encrypted in advanced cases)
JWTs and Standards
JWT is standardized under RFC 7519 (published by the IETF), which defines the token structure and how claims are represented.
JWT Authentication vs. JWT Authorization (Common Misunderstanding)
A JWT is not “authentication” by itself. It’s evidence that authentication happened somewhere-issued by an identity provider after successful login.
In most modern systems:
- Authentication happens at the Identity Provider (IdP)
- Authorization decisions happen at the API / resource server, using the token’s claims and policies
Example
A token may include:
sub: user identifierexp: expirationiss: issuer (who created the token)aud: audience (who the token is meant for)scope: permissions likeread:invoices- custom claims like
roles: ["finance_admin"]
Your API validates the token and then checks whether the requested endpoint requires read:invoices or a specific role.
Auth0: Where It Fits (And What It Actually Does)
Auth0 is an identity platform (an IdP and CIAM solution) that helps teams implement authentication flows and issue tokens (often JWTs) for accessing applications and APIs.
Auth0 typically helps with:
- User authentication (database users, social login, enterprise SSO)
- Multi-factor authentication (MFA)
- Token issuance (ID tokens and access tokens)
- Sessions, refresh tokens, rotation, and security controls
- Rules/actions for customizing identity workflows
- Integrations with applications and APIs
Auth0 Is Not “Authorization for Everything”
Auth0 can store roles/permissions and include them as token claims, but fine-grained authorization (especially contextual or resource-level) is usually enforced at the API layer or via a dedicated policy engine.
How JWT, IAM, and Auth0 Work Together (Typical Architecture)
Here’s the common flow for a web or mobile app calling an API:
- User signs in via Auth0 (authentication)
- Auth0 issues an access token (often a JWT)
- The app calls your API with:
Authorization: Bearer
- Your API:
- validates the JWT signature (trust)
- verifies
iss,aud,exp(correctness) - checks scopes/roles/claims (authorization)
- API returns data only if permitted
Best Practice Note
Even with JWTs, APIs should still enforce authorization at the endpoint and resource level. Never rely solely on the frontend to “hide” admin features.
Real-World Authorization Models You’ll See with JWT-Based Systems
RBAC (Role-Based Access Control)
Users get roles like admin, manager, viewer. Roles map to permissions.
- Simple and common
- Can become rigid if permissions vary by context
ABAC (Attribute-Based Access Control)
Decisions consider attributes such as department, location, risk score, device trust, or data classification.
- Flexible and powerful
- More complex to implement and audit
Scopes (OAuth 2.0 Style)
Tokens carry scopes like read:orders or write:orders.
- Great for API access control
- Needs consistent scope design across services
Many mature systems combine these: roles for coarse access, scopes for API operations, and ABAC policies for sensitive decisions.
Security Essentials: Doing JWT and IAM the Right Way
1) Validate Tokens Properly
APIs should verify:
- Signature (using correct algorithm and key)
- Issuer (
iss) - Audience (
aud) - Expiration (
exp) and clock skew - Token type and scopes/roles
2) Keep JWTs Short-Lived
Short expiration reduces blast radius if a token is stolen. Use refresh tokens carefully, especially on mobile and SPAs.
3) Don’t Put Secrets in JWT Payloads
JWT payloads are encoded, not encrypted (unless you use JWE). Treat claims as readable by anyone holding the token.
4) Avoid “Authorization by JWT Claim Alone”
Claims are inputs to authorization-not the full policy. Resource-level checks still matter:
- Can the user access this specific invoice ID?
- Are they allowed to access data for this tenant?
5) Design for Revocation and Risk
JWTs are stateless, which is efficient-but revocation is harder. Consider strategies like:
- short token lifetimes
- rotating refresh tokens
- centralized session tracking for high-risk apps
- token introspection or deny-lists when needed
Where Intelligent Document Processing Fits Into Secure Workflows
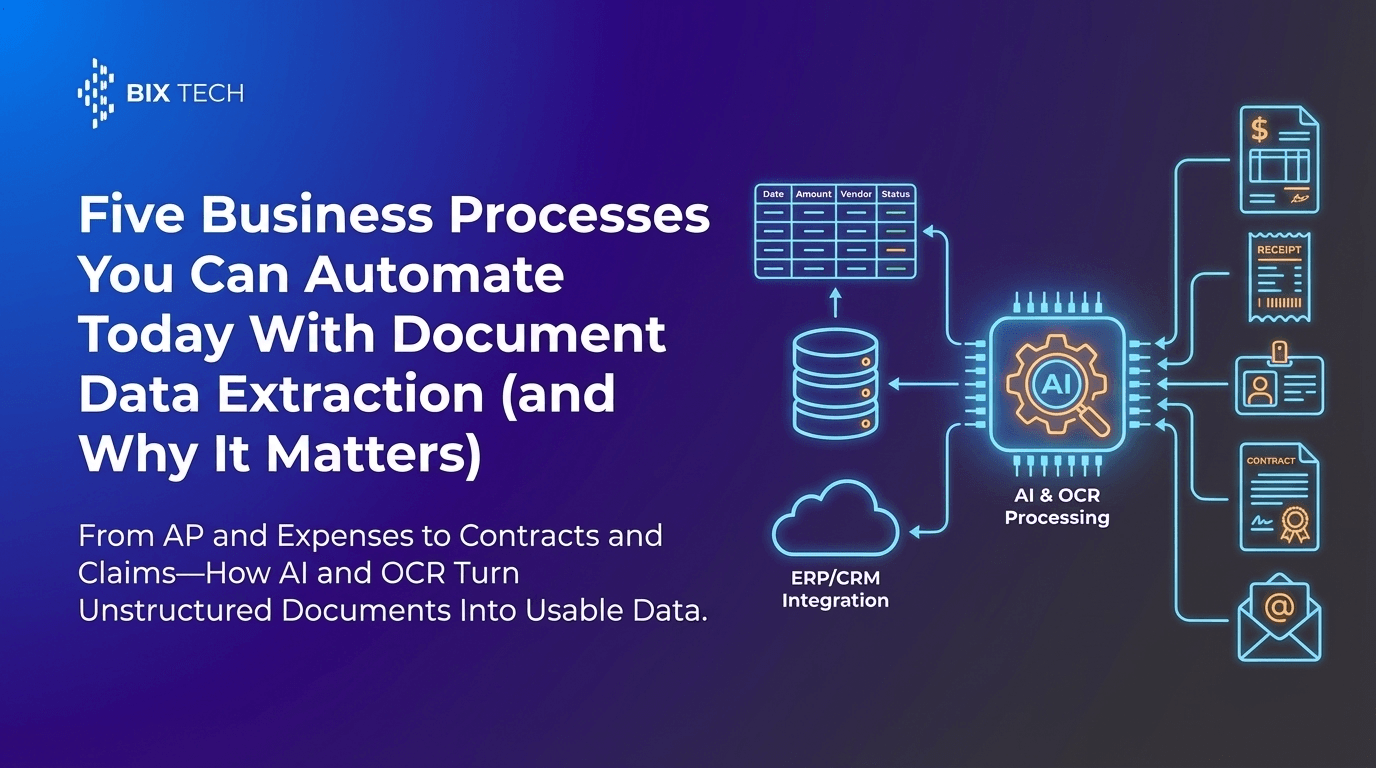
Many organizations first encounter serious IAM and authorization complexity when they digitize high-volume, sensitive workflows-especially documents like invoices, receipts, contracts, and identity documents.
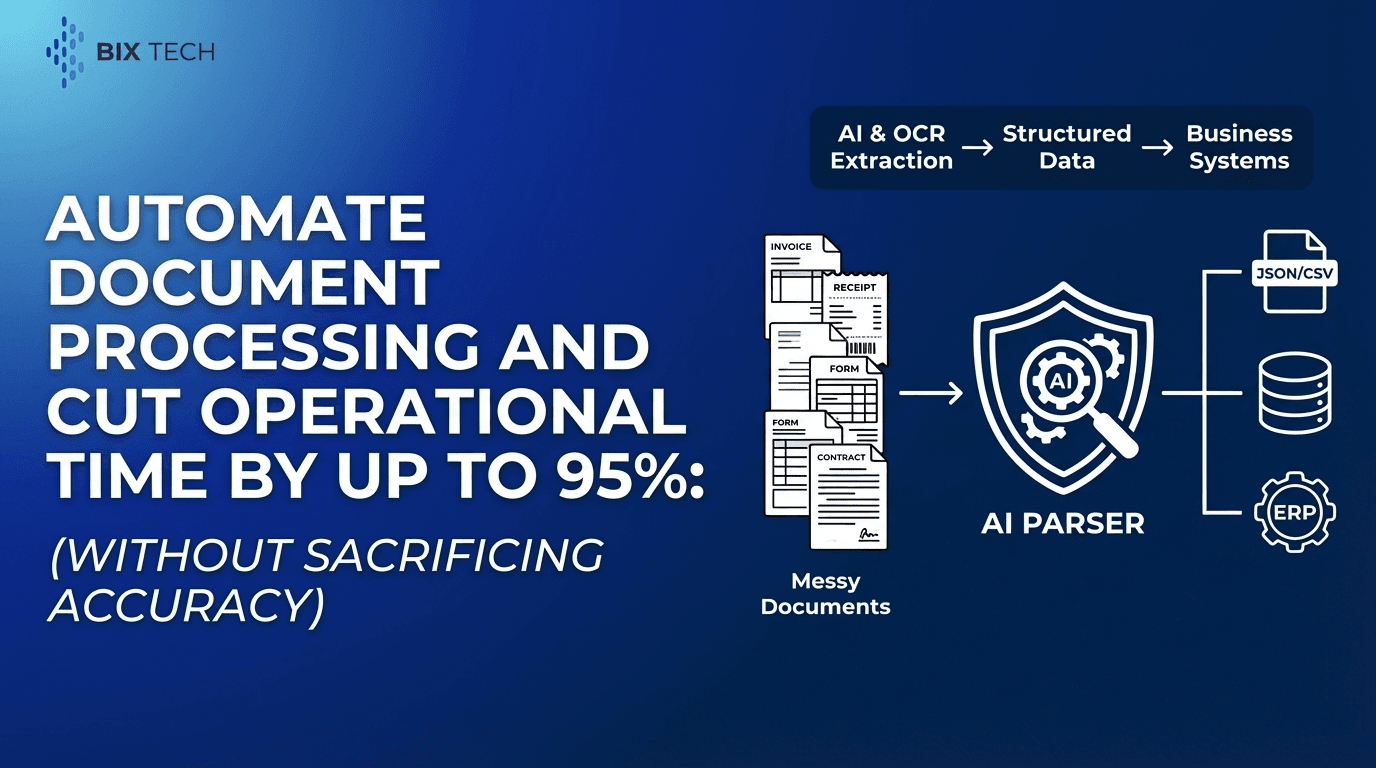
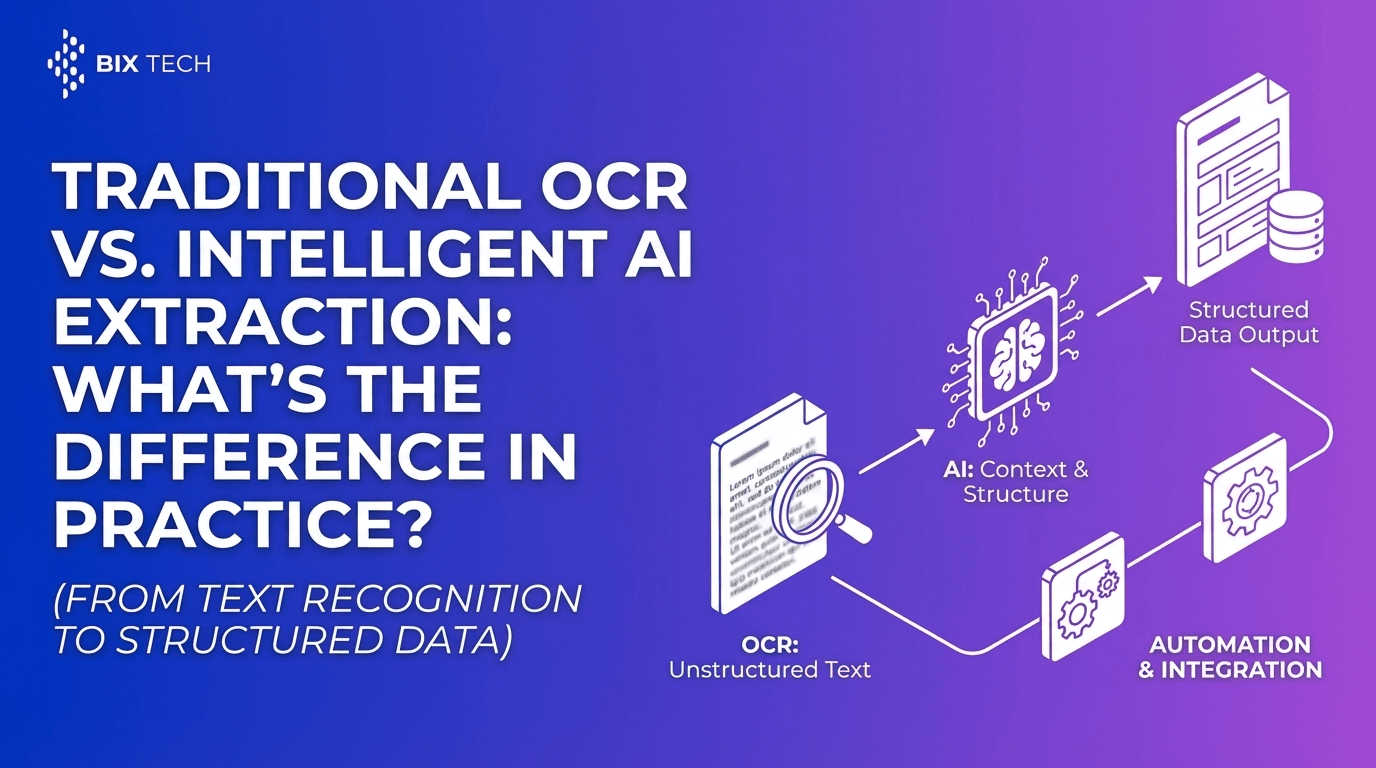
That’s where an intelligent document processing solution like Parser becomes strategic: it automates extraction of structured data from unstructured or semi-structured documents using AI and OCR, reducing manual data entry while improving speed and accuracy. For a deeper look at automation trends, see OCR extraction in 2026.
Why Authentication and Authorization Matter in Document Automation
Document-heavy processes often involve:
- PII (names, addresses, IDs)
- financial data (bank details, invoice totals)
- contractual terms (signatures, obligations)
Secure access must ensure:
- only authorized roles can upload or view certain document types
- extracted fields are written only to permitted systems (ERP/CRM/databases)
- audit trails exist for compliance
Parser at a Glance (Key Capabilities)
- Automated Data Extraction: Converts invoices, receipts, contracts, and IDs into actionable digital data
- AI-Powered Accuracy: Learns layouts and context for diverse formats
- Customizable Workflows: Define the fields and rules that matter to your business
- Integration Ready: Connect with ERPs, databases, and BI tools for an end-to-end pipeline
- Scalable: Handles high volumes efficiently as operations grow
When integrated into an IAM-aware architecture (SSO, scoped API access, role-based permissions), document automation becomes both fast and governed. To understand the platform foundation, explore the Parser overview.
Common Questions (Featured Snippet–Friendly)
What is the difference between JWT and OAuth?
JWT is a token format. OAuth 2.0 is an authorization framework that defines how clients obtain access to APIs. OAuth access tokens can be JWTs, but they don’t have to be.
Is Auth0 an IAM solution?
Auth0 is an identity platform commonly used for authentication, SSO, and token issuance. In many organizations, it functions as a key part of an IAM strategy, especially for customer identity and application authentication.
Does a JWT prove a user is authenticated?
A JWT can indicate that authentication occurred if it was issued by a trusted identity provider. Your API must validate the token and then enforce authorization rules before granting access.
What should be stored in a JWT?
Store only what the API needs to make decisions-user ID, issuer, audience, expiration, scopes/roles, and minimal necessary claims. Avoid sensitive data unless the token is encrypted and the design explicitly requires it.
Bringing It All Together
- IAM is the overarching approach to identity and access across systems.
- Authentication confirms identity; authorization controls permissions.
- JWT is a widely used, verifiable token format for transmitting claims-often used as an OAuth access token.
- Auth0 helps implement secure authentication and token-based access at scale.
- In high-volume workflows-especially those involving sensitive documents-pairing strong IAM with automation tools like Parser can deliver both efficiency and compliance. If security and compliance are top priorities, review Parser’s data security approach.
Done well, JWT, IAM, and Auth0 aren’t just security buzzwords-they’re the foundation for scalable, secure digital operations.